A Practical Guide to Conducting Vulnerability Assessments
In today’s digital world, cyber threats continue to evolve, making it crucial for businesses of all sizes to proactively identify and address security weaknesses. A vulnerability assessment is a systematic process that helps organizations detect, analyze, and mitigate potential security gaps before cybercriminals can exploit them.
This guide will walk you through the fundamentals of vulnerability assessments, breaking down the process in a way that both technical and non-technical audiences can understand. By the end, you will know how to conduct an effective vulnerability assessment to protect your business from cyber threats.
What is a Vulnerability Assessment?
A vulnerability assessment is a proactive approach to identifying and evaluating security weaknesses in an organization’s IT infrastructure, applications, and processes. It helps businesses prioritize risks and implement measures to prevent cyberattacks. Unlike penetration testing, which actively exploits vulnerabilities, a vulnerability assessment focuses on discovering and assessing security gaps.
Why is it Important?
- Prevents cyberattacks by identifying weaknesses before attackers do.
- Reduces financial losses associated with data breaches and system downtime.
- Ensures compliance with industry regulations and security standards.
- Builds trust with customers by demonstrating a commitment to cybersecurity.
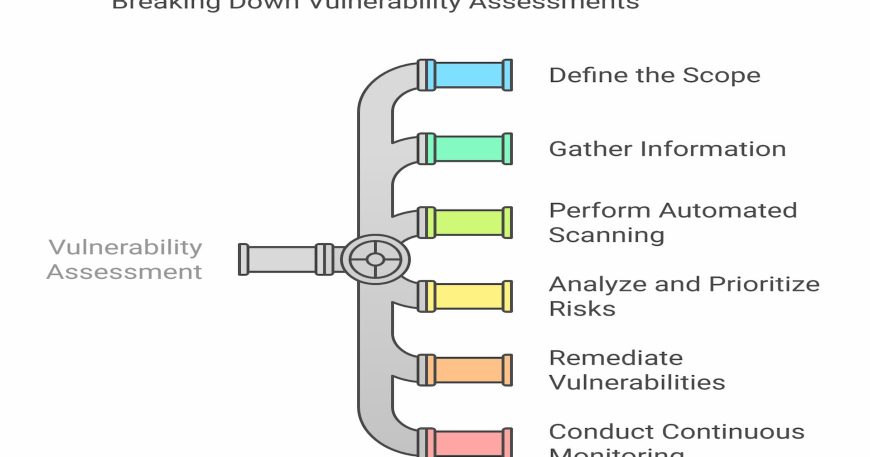
Step-by-Step Guide to Conducting a Vulnerability Assessment
Step 1: Define the Scope
Before starting an assessment, clearly define what you will evaluate. Consider:
- Network infrastructure (firewalls, routers, servers, workstations, cloud services)
- Applications (web applications, databases, software)
- Endpoints and devices (laptops, mobile devices, IoT devices)
- Internal and external threats
Step 2: Gather Information
Understanding your IT environment helps in identifying potential weaknesses.
- Conduct an asset inventory to list all hardware and software components.
- Map out network architecture to visualize attack surfaces.
- Identify security policies and compliance requirements.
Step 3: Perform Automated Scanning
Use vulnerability scanning tools to detect security weaknesses. Popular tools include:
- Nessus (network and system scanning)
- OpenVAS (open-source vulnerability scanning)
- Qualys (cloud-based scanning and compliance monitoring)
- Burp Suite (web application security testing)
Step 4: Analyze and Prioritize Risks
Not all vulnerabilities pose the same level of risk. Use the Common Vulnerability Scoring System (CVSS) to categorize threats based on:
- Severity (low, medium, high, critical)
- Potential impact on operations
- Likelihood of exploitation
Step 5: Remediate Vulnerabilities
After identifying vulnerabilities, take action to mitigate them:
- Apply security patches for outdated software and operating systems.
- Strengthen configurations for firewalls, network access controls, and system settings.
- Enhance authentication methods by enforcing multi-factor authentication (MFA).
- Educate employees about cybersecurity best practices to reduce human error risks.
Step 6: Conduct Continuous Monitoring
Vulnerability assessments should not be a one-time activity. Implement:
- Regular automated scans and manual reviews.
- Security awareness training for employees.
- Incident response plans to handle security breaches effectively.
Common Challenges and How to Overcome Them
1. Lack of Cybersecurity Awareness
Solution: Conduct regular security awareness training to educate employees on phishing attacks, weak passwords, and social engineering tactics.
2. Limited Budget and Resources
Solution: Prioritize vulnerabilities based on risk level and use cost-effective cybersecurity solutions tailored for SMBs.
3. False Positives in Scanning Results
Solution: Manually validate vulnerabilities to ensure that they are legitimate risks before remediation.
4. Keeping Up with Emerging Threats
Solution: Subscribe to threat intelligence feeds and continuously update security tools and policies.
Conclusion
Vulnerability assessments are essential for securing your business against cyber threats. By following a structured approach—defining scope, gathering information, scanning for weaknesses, prioritizing risks, and applying security measures—you can significantly reduce the chances of a cyberattack.
Need expert assistance in securing your IT infrastructure? CYBANITE provides tailored cybersecurity solutions to help businesses identify and mitigate risks effectively. Contact us today to strengthen your cybersecurity defenses! 🚀
#Cybersecurity #VulnerabilityAssessment #ITSecurity #SmallBusinessSecurity #TechForBusiness